In order to achieve below requirements, we have to use a mix of Symmetric (Secret) key algorithm & Asymmetric (Public/Private) key algorithm:
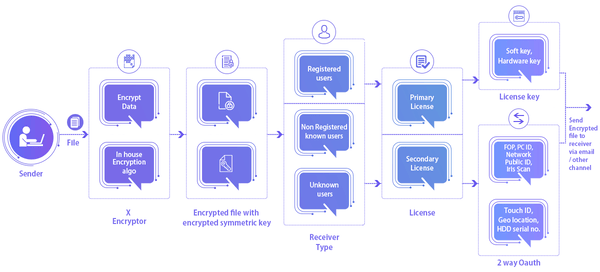
File is encrypted using Symmetric key as large volume of data should be encrypted with Symmetric key which is faster than Asymmetric key. But the symmetric key itself is not very secure. Thus, it is encrypted using Asymmetric key/Public key of receiver which is highly secure. As a result, we get an encrypted file with encrypted symmetric key.
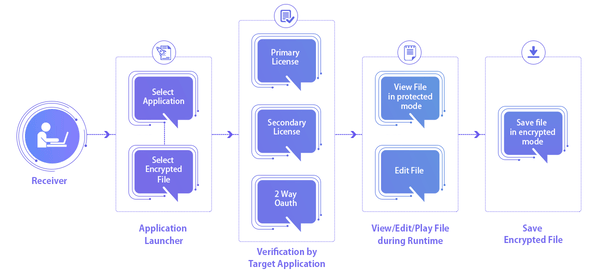
In order to decrypt the received file, the encrypted symmetric key is decrypted using private key of receiver. Then the encrypted file is decrypted using this symmetric key. As a result, we get decrypted file which is now ready to get opened in target application.
To perform any file related operation, user needs to authenticate himself via fingerprint scan. If fingerprint authentication is enabled by Sender, then receiver can access the encrypted docs by verifying his fingerprint. Fingerprints are unique, impossible to detect & difficult to fake without significant effort. When a fingerprint is scanned, Touch ID is generated & the device compares the stored value with scanned value. If fingerprint matches successfully, receiver will be able to open the doc.

To perform any file related operation, user needs to authenticate himself via Iris scan. If Iris authentication is enabled by Sender, then receiver can access the encrypted docs by authenticating his iris. When iris is scanned, Iris ID is generated & the device compares the current subject's iris with the stored value. If matched successfully, receiver will be able to open the doc.

In case the Sender wants his docs to be accessed in a particular region, he can do so by Setting up Lat, Long Coordinates of that location. Sender will encrypt the docs using X-encryptor tool & will enable location based authentication for those docs.
At the receiving end, if the PC of receiver lie within the authorized region, then only the encrypted docs will be accessible.
Computer geolocation can be performed by associating a geographic location with IP address location data can
include information such as country, region, city, postal/zip code, latitude, longitude, time zone to correctly track the real time position of user.

If OTP based authentication is enabled by Sender, OTP will be sent to Email ID/Mobile number of Receiver as applicable.
✔If OTP is sent to receiver's email ID, then receiver needs to verify the generated OTP first to access
the encrypted docs as sent.
✔ If OTP is sent to receiver's mobile number, then as in above case, he needs to verify the generated OTP
first to access the encrypted docs as sent.

If this type of authentication is enabled, then an OTP will be sent to Sender's mobile number whenever the receiver wants to access the encrypted document as shared by Sender. Once approval/confirmation is provided by the Sender Fingerprint/Iris scan or Pattern lock /Password [as per device features] , then only receiver will be able to open the encrypted document Receiver can't open the document unless OTP is verified by Sender.

After encrypting the data using X-encryptor tool, in order to send it to intended recipients, the sender can configure the HDD Serial numbers of receiver's PCs so that the data will get decrypted only on PCs having HDD with serial numbers as configured by Sender. When the receiver tries to open the encrypted document in target application using Launcher, Hard Disk Serial Number will be verified & if matched successfully, the document will open.
After encrypting the data using X-encryptor tool, in order to send it to receivers, the sender can configure the PC IDs of receiver's PC so that the data will get decrypted only on PCs having authorized PC IDs.Sender can configure these IDs to provide access only on those PCs.When the receiver tries to open the encrypted document in target application using Launcher, PC ID will be verified & if matched successfully, the document will open.

When a license is purchased, then a key is linked to that license which is used to activate the product after installation. This key is unique for every license.
If the sender wishes to send encrypted docs to the receivers who have bought different packages but share similar Client ID, he needs to configure the activation keys of selected receivers. Activation keys must be known to Sender to achieve this.
At the receiving end, if configured Activation key matches with that of receiver, then only he will be able to access the encrypted docs.

When a Sender wants that the encrypted docs should be accessible to all the PCs connected within a network, then the Sender
will enable Network based authentication. After encrypting the docs, Sender will configure the Networks in which docs will
be accessible by defining Network IDs .
At the receiving end, when the receiver tries to access the encrypted docs, the system will scan the PCs which fall under
authorized networks & if verified successfully, Encrypted docs will open in respective target application under authorized networks.
There are cases where a Sender wants that the encrypted docs should be accessible on individual PCs connected within a network.
Sender will enable the authentication for Standalone PCs after encrypting the docs by configuring Public Ids of those PCs. To every PC,
Public ID is linked which is unique. Thus, the required Public Ids of receiver's PCs should be known to enable this type of authentication.
At the receiving end, when the receiver tries to access the encrypted docs, the system will scan the PCs with Ids configured in 2-way authentication & if verified successfully, Encrypted docs will open in target application.
After encrypting the data using X-encryptor tool, a random password is set by the Sender to open the encrypted document & shared with intended recipient(s). When the receiver wants to open the document using Launcher, system asks for “File Open Password (FOP)” as enabled by Sender. The receiver needs to enter the correct FOP in order to open the doc. After successful authentication, file gets opened in target application. The FOP can be shared with receiver online via any medium or offline.

To add an extra level of security, If the Sender wants that the encrypted docs should be accessible on a specific day(s) of the week/between defined date(s) & during defined time interval, then the required authentications can be enabled by choosing the options.
If a specific day of the week was selected, then the encrypted file will be accessible by the receiver on that day of every week
between dates as defined by Sender.
If only Start date & End date were defined, then the encrypted file will be accessible by the receiver between those dates only.
If the time period was also defined, then the encrypted file will be accessible during that time period only on defined day(s)/dates if applicable.

If the Sender wants to share encrypted data with unknown receivers, then he can enable authentications for remote access. Under this, the Sender needs to select the types of authentications which need to be verified by unknown receiver in order to access the shared encrypted data. If applicable, the receiver needs to make payment for downloading docs after providing basic information to the Sender.